On a recent test I came across a reflective XSS condition within a file upload page. When the extension was deemed invalid by the application, it was returned unsanitised within the error message. Not only did this turn out to be an exercise in exploiting reflective XSS in multipart/form-data but there were some pretty hefty restrictions on allowed characters too. Worthy of a post I thought. Continue reading
Category Archives: Web Applications
DOM XSS by Misusing Bootstrap
First of all, let me make it clear that this article is not about XSS in Bootstrap itself (the very popular libraries originally from Twitter to fancify your website), it’s about XSS as a result of using Bootstrap in an insecure fashion. It’s based on a real penetration test – the site in question wasn’t vulnerable but it was immediately clear how things could have gone wrong. I thought it would be an interesting XSS article, being both DOM-based and making use of a big-name library like Bootstrap. Continue reading
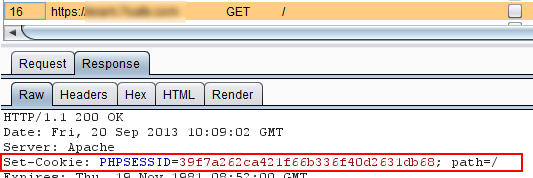
A Rough Guide to the Secure Cookie
On a recent pentest, I reported that the session management cookie was not being set with the secure flag (surprise, surprise)…
But in this case it didn’t seem to matter so much. Why? Because port 80 was shut: the whole application was served over HTTPS so the cookie would never have the chance to escape over HTTP, even if an attacker could engineer such a scenario – for example, by enticing the victim to click on a HTTP link (although more on this shortly). This is because the TCP connection must be set up with the 3-way handshake before any application data is sent over it – and since the port was closed, the connection falls at the first hurdle [1]. Continue reading
How To Improve Password Storage Security Right Now
In episode 120 of the TechSNAP podcast [skip 20 mins in], hosts Chris and Allan were discussing the breach of the Ubuntu Forums last month, when 1.82 million account details were estimated to have been at risk. According to Ars Technica, MD5 hashing was in place with a per-user salt. But whether you’ve got plaintext passwords, unsalted hashes, or single-iteration hashing, it’s time to upgrade. Chris and Allan discussed this issue, noting that when a user logs in, the web application has the plaintext password so that’s the opportunity to store the password using the new algorithm; users who haven’t logged in for a while will just have to wait. Of course, it doesn’t have to be this way, you can be a lot more proactive – and I’m sure Chris and Allan, who were just speaking off the cuff, would realise that too with a moment’s thought. Continue reading
Sophie – a web SQL shell
If you can exploit a flaw to upload files to an executable directory in an IIS environment, there are plenty of web shells around (some of which may be trojaned but that’s another issue) to give you an interactive command prompt via your browser. If the application makes use of a MS-SQL database, the same flaw can be used to upload Sophie, a “web SQL shell”, giving you access to the database via your browser as well: Continue reading